[홈서버 구축기] SSL 인증서 만들기 (연습)
관련 용어 정리
- SSL (Secure Socket Layer): Netscape에서 개발하여 SSLv3까지 개발되고 이후로는 TLS로 계승된다.
- TLS (Transport Layer Security): SSL3.0의 업그레이드 버전으로 시작. 현재 TLS1.2가 최신이고 TLS1.3이 개발 중이다.
- HTTPS (HTTP + Secure)
- CSR (Certificate Signing Request): 인증 서명 요청. 인증서명요청 파일의 확장자로 쓰인다.
- CRT : Certificate (인증서)의 약자. 보통 인증서 파일의 확장자로 쓰인다.
- CA (Certificate Authority): 공인인증기관.
- PKI (Public Key Infrastructure) : 공개키 기반구조
- PKCS (Public Key Cryptography Standards) : 공개키 암호화 표준
- PKCS #12 : 암호화 관련 파일 포맷 정의. 인증서와 개인키가 함께 들어있다.
- X.509 : 공개키 기반 인증서 형식 표준
- PEM (Privacy-enhanced Electronic Mail) : 인증서 형식의 하나 (Base64 Encoded DER certificate). 해당 형식 인증서의 확장자로 쓰인다.
- PFX (Personal inFormation eXchange) : PKCS#12 형식의 인증서 확장자로 쓰임
- P12 : PKCS#12 형식의 인증서 확장자로 쓰임
인증서를 만드는 방법에는 몇가지 있다.
- Self-signed 인증서
- CSR 명시적 생성 -> 인증서에 self-sign -> 인증서 완성
- CSR을 명시적으로 생성하지 않고, key와 부가정보들을 입력하여 직접 self-sign 하여 인증서 완성
- CSR (인증서 서명 요청)을 만들어 CA에 요청해서 발급받는 방법
- 유료
- 무료 (ex: Letsencrypt)
이 모두 공개키 기반 구조이므로 개인키부터 만들어서 진행해야한다.
순서는 아래와 같다.
- 개인키를 만든다.
- 옵션으로 암호를 부여할 수도 있다. (대칭키 암호화 알고리즘 적용)
- 암호가 들어있으면 서비스 구동시마다 암호를 물어봐서 암호를 제거하는게 편하다.
- 생성시부터 암호를 안넣는 방법도 있고
- 암호를 제거하는 방법도 있다. (아래 기술)
- 암호가 없는 경우 key 파일의 보안에 더욱 신경써야함
- 별도로 개인키와 쌍이 되는 공개키를 추출하는 방법도 있다. (아래 기술)
- 옵션으로 암호를 부여할 수도 있다. (대칭키 암호화 알고리즘 적용)
- CSR (인증서명요청. Certificate Signing Request)을 만든다.
- CSR을 만들때 input으로 개인키를 넣는 방법도 있고,
- CSR을 만들며 개인키도 함께 만드는 방법도 있다.
- 참고로 CSR안에는 공개키가 들어있는데 공개키는 명시적으로 만들지 않고 CSR 만들며 자동으로 생성되어 CSR안에 들어간다.
- 인증서를 만든다.
- Self sign 으로 만드는 방법
- Input으로 CSR을 명시적으로 넣어 인증서를 생성하는 방법
- CSR을 넣지 않고 암묵적 이용으로 인증서를 생성하는 방법
- CA에 인증서를 보내 요청하는 방법
- Self sign 으로 만드는 방법
하나씩 연습을 해본다.
Contents
개인키 만드는 방법 (참고 man genrsa)
– 암호없이 생성
# openssl genrsa -out <키이름> <비트 수>
ex) # openssl genrsa -out cert.key 2048
Generating RSA private key, 2048 bit long modulus
............................+++
...........................+++
e is 65537 (0x10001)
– 암호를 부여하여 생성 (대칭키 암호화 알고리즘 적용)
# openssl genrsa -<암호화알고리즘> -out <키이름> <비트수>
ex) # openssl genrsa -aes256 -out cert.key 2048
Generating RSA private key, 2048 bit long modulus
...............................................................+++
................................................+++
e is 65537 (0x10001)
Enter pass phrase for cert.key:
Verifying - Enter pass phrase for cert.key:
– 생성된 개인키를 보면 —-BEGIN RSA PRIVATE KEY— 로 시작한다.
# cat cert.key
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-256-CBC,68BA14C1149922156FA75CB1C7A11861
+oCHeV0RjCtCwVn6ooYYcY996XytwUxUWYF7IKrttvSWoALwe3NavX9SXvXeXh8j
JfuzQz4i5cybUwY/ZnYs3qWNUpdX6NfPMpZhnsL4O5LOLX3jIS0rnp+y/fLhnWQw
nkt3ta+Jh//AFOeP8+XCmFjI7uuA6pgRVfxKkEbq2eopmt0/vpMTpYbH5E6/foGP
eo1nSzfV2/PePEQRD4FeeD9/6w7JAmLGMuPb8nFNyLlce8avah1MucV+7lwsiAMR
TOA7+wHwvK6SZjvue6sSKrVkezOK9TG3sa/aWIq+uaMRfpuHCtHi8rj1hvUFYhXd
.... <중간 생략> ....
VDVlh98CgYBvJnsnADhZRwB2sC72XM2kKojaGNxmt0xahuGhmmGoityTgesIHM3a
j9BUz+w6rH5BC1t3LLsKVDj1DZ/LYO0K9fanayjPZJGWUeg3YMKP3CQi5TvqN54O
k9pjSxY+llSr3j8kLxzrPrsEDRbMiiBGIuouLMMx6Yl/ElbGI0VxGw==
-----END RSA PRIVATE KEY-----
– 생성된 개인키 정보 보기
ex) # openssl rsa -text -in cert.key
Enter pass phrase for cert.key:
Private-Key: (2048 bit)
modulus:
00:b7:48:7b:56:ee:6c:85:cc:84:de:07:51:39:b0:
35:72:79:fd:c9:02:37:79:79:21:94:3f:95:3e:1f:
b7:3a:ac:d2:c8:a2:08:b1:72:b3:d4:5b:9b:a6:f6:
f2:8e:08:fc:02:a7:e4:26:a9:90:1a:fc:c4:cd:53:
ae:7f:f7:3e:6b:d5:01:e0:14:e9:97:68:79:0d:8a:
61:1d:07:c2:2f:19:f0:8b:92:53:5d:8c:13:cd:ab:
50:43:56:21:85:66:4d:56:c4:6d:a3:c5:91:9a:9d:
db:66:a1:ea:a4:0f:4c:59:c9:7c:7d:06:bb:55:05:
42:0f:c8:03:bd:ec:5f:eb:af:ff:e4:a4:47:35:ca:
<이하 생략>
– 개인키와 쌍이 되는 공개키 뽑아내기
# openssl rsa -in <개인키 파일> -pubout -out <공개키 파일>
ex) # openssl rsa -in cert.key -pubout -out cert_pub.key
Enter pass phrase for cert.key:
writing RSA key
– 공개키 파일 내용 보기 (—-BEGIN PUBLIC KEY—- 로 시작)
ex) # cat cert_pub.key
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAt0h7Vu5shcyE3gdRObA1
cnn9yQI3eXkhlD+VPh+3OqzSyKIIsXKz1Fubpvbyjgj8AqfkJqmQGvzEzVOuf/c+
a9UB4BTpl2h5DYphHQfCLxnwi5JTXYwTzatQQ1YhhWZNVsRto8WRmp3bZqHqpA9M
Wcl8fQa7VQVCD8gDvexf66//5KRHNco3hOlHEw4rZA5Xxz87Wn7Gdok/QJ9ng82s
OA3lr3FMusSpVLACr+PcGxL6g6pf+dsbws53UmKg4t+OPXMtC/1AjvvvirpW2fHc
CVsYwbP5uF0UDb3IlpTHOC3E9iYzGqZjSN8RSoemm+iUZJhmJYexS4p9iVBEJ2DG
CwIDAQAB
-----END PUBLIC KEY-----
– 비밀번호가 걸려있는 개인키에서 비밀번호 제거하기
# openssl rsa -in <개인키파일> -out <새로저장할비번없는개인키파일>
ex) openssl rsa -in cert.key -out cert_nopass.key
Enter pass phrase for cert.key:
writing RSA key
– 비밀번호 없는 개인키에 비밀번호 부여하기
# openssl rsa -in <비번없는개인키파일> -out <새로저장할비번있는개인키파일> -<암호화방법>
ex) # openssl rsa -in cert_nopass.key -out cert_pass.key -aes256
writing RSA key
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
CSR 만드는 방법 (참고: man req)
- 위에서 만든 개인키를 입력으로 넣는 방법
- #openssl req -new -key <개인키> -out <CSR 파일>
ex> # openssl req -new -key cert.key -out cert.csr
Enter pass phrase for cert.key:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:KR
State or Province Name (full name) [Some-State]:Seoul
Locality Name (eg, city) []:Gangnam
Organization Name (eg, company) [Internet Widgits Pty Ltd]:hangadac.com
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:blog.hangadac.com
Email Address []:myemail_address@gmail.comPlease enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
- 개인키도 함께 만드는 방법
- # openssl req -new -out <CSR 파일> -keyout <개인키 파일> -newkey rsa:<키 비트수>
ex) # openssl req -new -out cert.csr -keyout cert.key -newkey rsa:2048
Generating a 2048 bit RSA private key
.........................................................................................................+++
..................................................................................................+++
writing new private key to 'cert.key'
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:KR
State or Province Name (full name) [Some-State]:Seoul
Locality Name (eg, city) []:Gangnam
Organization Name (eg, company) [Internet Widgits Pty Ltd]:hangadac.com
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:blog.hangadac.com
Email Address []:myemail_address@gmail.comPlease enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
- 인증서 정보 보기
- # openssl req -text -in <인증서 파일명> -noout
ex) # openssl req -text -in cert.csr -noout
Certificate Request:
Data:
Version: 0 (0x0)
Subject: C=KR, ST=Seoul, L=Gangnam, O=hangadac.com, CN=blog.hangadac.com/emailAddress=myemail-address@gmail.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:af:5f:f7:ae:20:ee:4e:d0:61:d2:25:9b:dc:cf:
b6:a0:24:98:93:5e:33:d4:ce:b0:e5:fd:5a:2c:7c:
50:c6:dc:ae:5a:4c:bd:ff:11:88:71:73:d3:f1:04:
0b:d2:b4:51:f1:2e:2f:12:88:46:9f:1c:47:2e:2a:
33:cf:e2:9b:58:04:73:20:da:8b:16:a4:2a:ae:1f:
20:e0:f2:ba:4e:c9:80:78:3f:14:3f:8b:fb:dd:a6:
95:77:95:e0:2d:03:f4:89:2f:3d:2b:3c:9c:26:e6:
1e:67:d9:66:b2:42:d0:c6:c3:f7:4f:60:b1:d2:86:
0a:1c:90:b7:dd:fb:b3:ac:33:de:e1:db:d1:7d:49:
47:30:4f:3a:d3:2f:d7:4b:50:d6:62:3d:6d:de:8f:
92:14:87:7b:71:aa:00:d2:c4:21:79:3e:be:96:2b:
d0:27:bd:cb:c1:8e:30:78:a2:75:a4:a8:52:7f:c8:
ce:53:7e:1d:3d:18:1c:d7:d1:19:13:f2:3c:cd:f3:
4b:cc:aa:81:41:f4:0c:a6:0f:82:60:e5:03:2a:d1:
35:a4:ff:07:b8:2a:59:8f:0e:89:3a:a8:61:6d:fd:
c8:b1:1d:7d:4d:f7:d3:b3:ee:30:10:c9:9f:bb:59:
5c:6e:1f:5c:06:d0:1d:5d:d1:40:a4:b9:12:17:92:
56:2b
Exponent: 65537 (0x10001)
Attributes:
a0:00
Signature Algorithm: sha256WithRSAEncryption
3b:1c:8a:51:de:40:57:26:f9:1c:3f:44:e6:4e:30:f4:ea:5b:
cb:a7:52:20:dc:9a:7f:84:6a:28:d8:a2:83:49:8e:3f:95:98:
33:d1:7e:f1:23:6f:6a:67:ef:31:96:ce:d1:ef:74:7b:18:28:
32:ee:6d:bc:a5:fc:07:ae:b9:b2:35:83:58:93:42:a2:db:71:
9a:6a:5f:56:52:67:03:3e:96:b6:20:cd:14:a3:24:af:64:26:
f7:08:d7:11:11:69:8a:64:c3:99:3b:00:c6:3e:57:65:0f:3d:
8f:1f:b7:c2:cb:56:1d:45:9d:0c:aa:29:04:e6:ee:79:b5:c1:
be:cd:4c:16:2e:56:fa:21:a2:59:41:c6:ca:0d:24:03:6f:87:
fa:f5:87:42:bb:a4:17:e4:47:67:3e:ae:f2:a6:9e:7c:16:13:
05:bb:4a:bc:2e:8f:4c:32:94:82:a9:19:02:29:08:9f:37:9c:
40:20:27:b5:e6:3f:dd:32:22:09:15:1e:69:65:d4:1a:82:ae:
5d:15:ea:7e:9f:9b:3a:43:32:a8:33:06:be:85:b8:13:26:3c:
b6:9a:12:4e:3f:93:cc:b0:86:f8:e3:9d:0f:34:0f:07:73:ff:
fa:af:4c:c6:15:01:c2:21:0c:ed:0b:2d:fe:c0:b0:4b:b7:dc:
f3:6f:78:03
Self Signed 인증서 만드는 방법
- CSR을 명시적으로 넣어 인증서를 만드는 방법
- # openssl x509 -req -days <유효날수> -in <인증사인요청파일> -signkey <개인키> -out <인증서 파일명>
ex) # openssl x509 -req -days 365 -in cert.csr -signkey cert.key -out cert.crt
Signature ok
subject=/C=KR/ST=Seoul/L=Gangnam/O=hangadac.com/CN=blog.hangadac.com/emailAddress=myemail-address@gmail.com
Getting Private key
Enter pass phrase for cert.key:
- CSR을 넣지 않고 (암묵적으로 CSR을 생성/이용하여) 인증서를 만드는 방법
- # openssl req -new -x509 -days <유효날수> -key <개인키> -out <인증서파일명>
ex) # openssl req -new -x509 -days 365 -key cert.key -out cert.crt
Enter pass phrase for cert.key:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:KR
State or Province Name (full name) [Some-State]:Seoul
Locality Name (eg, city) []:Gangnam
Organization Name (eg, company) [Internet Widgits Pty Ltd]:hangadac.com
Organizational Unit Name (eg, section) []:
Common Name (e.g. server FQDN or YOUR name) []:blog.hangadac.com
Email Address []:myemail_address@gmail.com
- 인증서 파일 내용 보기
- # cat <인증서 파일명>
ex) # cat cert.crt
-----BEGIN CERTIFICATE-----
MIID7TCCAtWgAwIBAgIJAJRKKwYSJLVeMA0GCSqGSIb3DQEBCwUAMIGMMQswCQYD
VQQGEwJLUjEOMAwGA1UECAwFU2VvdWwxEDAOBgNVBAcMB0dhbmduYW0xFTATBgNV
BAoMDGhhbmdhZGFjLmNvbTEaMBgGA1UEAwwRYmxvZy5oYW5nYWRhYy5jb20xKDAm
BgkqhkiG9w0BCQEWGW15ZW1haWxfYWRkcmVzc0BnbWFpbC5jb20wHhcNMTcwNzI4
MDY1MjU3WhcNMTgwNzI4MDY1MjU3WjCBjDELMAkGA1UEBhMCS1IxDjAMBgNVBAgM
BVNlb3VsMRAwDgYDVQQHDAdHYW5nbmFtMRUwEwYDVQQKDAxoYW5nYWRhYy5jb20x
GjAYBgNVBAMMEWJsb2cuaGFuZ2FkYWMuY29tMSgwJgYJKoZIhvcNAQkBFhlteWVt
YWlsX2FkZHJlc3NAZ21haWwuY29tMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIB
CgKCAQEAr1/3riDuTtBh0iWb3M+2oCSYk14z1M6w5f1aLHxQxtyuWky9/xGIcXPT
8QQL0rRR8S4vEohGnxxHLiozz+KbWARzINqLFqQqrh8g4PK6TsmAeD8UP4v73aaV
d5XgLQP0iS89KzycJuYeZ9lmskLQxsP3T2Cx0oYKHJC33fuzrDPe4dvRfUlHME86
0y/XS1DWYj1t3o+SFId7caoA0sQheT6+livQJ73LwY4weKJ1pKhSf8jOU34dPRgc
19EZE/I8zfNLzKqBQfQMpg+CYOUDKtE1pP8HuCpZjw6JOqhhbf3IsR19TffTs+4w
EMmfu1lcbh9cBtAdXdFApLkSF5JWKwIDAQABo1AwTjAdBgNVHQ4EFgQU4gc/WOh1
vIFT/l1IjFB+oxgPxYswHwYDVR0jBBgwFoAU4gc/WOh1vIFT/l1IjFB+oxgPxYsw
DAYDVR0TBAUwAwEB/zANBgkqhkiG9w0BAQsFAAOCAQEAHJyXti4KpN53I+3Vj+QE
pHtvJWgh2OHOv+mZUB4pDlVercrMtBQNjOszv52fmibbwBWQ9UX0fPIHwESUNEvQ
/phdIQ8sKFYF+D3JbEXfBpQKW3g2zbSNYf7j10NBBwBHfKiyjsslqOzmfBxHygwl
uFj+ezNbfGlY6MdcE4NvYRhWbZf8YGLse+YZL+QLjtdvjjZsyfHyQ5WFK4ufJix/
I8Fnzp6viqsce6hFMjS/WxuTzLyzyjrizved3KZuY7Hn82j6zOg3XyHAHkkeZf+Y
yc+5/OBhab3nYoebcq8AuEPZz9LL8lN0scmmOTKQJR+oAhyM4A2cEGghD14FkzNY
qw==
- 인증서 정보 보기
- # openssl x509 -text -in <인증서파일명> -noout
ex) # openssl x509 -text -in cert.crt -noout
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
94:4a:2b:06:12:24:b5:5e
Signature Algorithm: sha256WithRSAEncryption
Issuer: C=KR, ST=Seoul, L=Gangnam, O=hangadac.com, CN=blog.hangadac.com/emailAddress=myemail_address@gmail.com
Validity
Not Before: Jul 28 06:52:57 2017 GMT
Not After : Jul 28 06:52:57 2018 GMT
Subject: C=KR, ST=Seoul, L=Gangnam, O=hangadac.com, CN=blog.hangadac.com/emailAddress=myemail_address@gmail.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:af:5f:f7:ae:20:ee:4e:d0:61:d2:25:9b:dc:cf:
b6:a0:24:98:93:5e:33:d4:ce:b0:e5:fd:5a:2c:7c:
50:c6:dc:ae:5a:4c:bd:ff:11:88:71:73:d3:f1:04:
0b:d2:b4:51:f1:2e:2f:12:88:46:9f:1c:47:2e:2a:
33:cf:e2:9b:58:04:73:20:da:8b:16:a4:2a:ae:1f:
20:e0:f2:ba:4e:c9:80:78:3f:14:3f:8b:fb:dd:a6:
95:77:95:e0:2d:03:f4:89:2f:3d:2b:3c:9c:26:e6:
1e:67:d9:66:b2:42:d0:c6:c3:f7:4f:60:b1:d2:86:
0a:1c:90:b7:dd:fb:b3:ac:33:de:e1:db:d1:7d:49:
47:30:4f:3a:d3:2f:d7:4b:50:d6:62:3d:6d:de:8f:
92:14:87:7b:71:aa:00:d2:c4:21:79:3e:be:96:2b:
d0:27:bd:cb:c1:8e:30:78:a2:75:a4:a8:52:7f:c8:
ce:53:7e:1d:3d:18:1c:d7:d1:19:13:f2:3c:cd:f3:
4b:cc:aa:81:41:f4:0c:a6:0f:82:60:e5:03:2a:d1:
35:a4:ff:07:b8:2a:59:8f:0e:89:3a:a8:61:6d:fd:
c8:b1:1d:7d:4d:f7:d3:b3:ee:30:10:c9:9f:bb:59:
5c:6e:1f:5c:06:d0:1d:5d:d1:40:a4:b9:12:17:92:
56:2b
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
E2:07:3F:58:E8:75:BC:81:53:FE:5D:48:8C:50:7E:A3:18:0F:C5:8B
X509v3 Authority Key Identifier:
keyid:E2:07:3F:58:E8:75:BC:81:53:FE:5D:48:8C:50:7E:A3:18:0F:C5:8BX509v3 Basic Constraints:
CA:TRUE
Signature Algorithm: sha256WithRSAEncryption
1c:9c:97:b6:2e:0a:a4:de:77:23:ed:d5:8f:e4:04:a4:7b:6f:
25:68:21:d8:e1:ce:bf:e9:99:50:1e:29:0e:55:5e:ad:ca:cc:
b4:14:0d:8c:eb:33:bf:9d:9f:9a:26:db:c0:15:90:f5:45:f4:
7c:f2:07:c0:44:94:34:4b:d0:fe:98:5d:21:0f:2c:28:56:05:
f8:3d:c9:6c:45:df:06:94:0a:5b:78:36:cd:b4:8d:61:fe:e3:
d7:43:41:07:00:47:7c:a8:b2:8e:cb:25:a8:ec:e6:7c:1c:47:
ca:0c:25:b8:58:fe:7b:33:5b:7c:69:58:e8:c7:5c:13:83:6f:
61:18:56:6d:97:fc:60:62:ec:7b:e6:19:2f:e4:0b:8e:d7:6f:
8e:36:6c:c9:f1:f2:43:95:85:2b:8b:9f:26:2c:7f:23:c1:67:
ce:9e:af:8a:ab:1c:7b:a8:45:32:34:bf:5b:1b:93:cc:bc:b3:
ca:3a:e2:ce:f7:9d:dc:a6:6e:63:b1:e7:f3:68:fa:cc:e8:37:
5f:21:c0:1e:49:1e:65:ff:98:c9:cf:b9:fc:e0:61:69:bd:e7:
62:87:9b:72:af:00:b8:43:d9:cf:d2:cb:f2:53:74:b1:c9:a6:
39:32:90:25:1f:a8:02:1c:8c:e0:0d:9c:10:68:21:0f:5e:05:
93:33:58:ab
공인인증서 만들기
- 각 CA (Certificate Authority) 별로 가이드를 제공함
- 추후 공짜 공인인증서 발급을 Letsencrypt를 통해 하겠음
- 참고로 이곳 hangadac.com도 Letsencrypt를 통해 공인인증서 발급 받았음
인증서 포맷 변경하기
- PEM -> DER 변환
- # openssl x509 -inform PEM -in <PEM 인증서> -outform DER -out <결과 DER 인증서>
- DER -> PEM 변환
- # openssl x509 -inform DER -in <DER 인증서> -outform PEM -out <결과 PEM 인증서>
- PEM -> PKCS#12(PFX) 변환
- # openssl pkcs12 -export -inkey <개인키> -in <PEM 인증서> -out <pfx 인증서>
- PKCS#12 (PFX) -> PEM 변환
- # openssl pkcs12 -in <pfx 인증서> -out <PEM 인증서> -nodes

 홈서버 SSD 교체 완료 (2019년 9월 24일)
홈서버 SSD 교체 완료 (2019년 9월 24일) 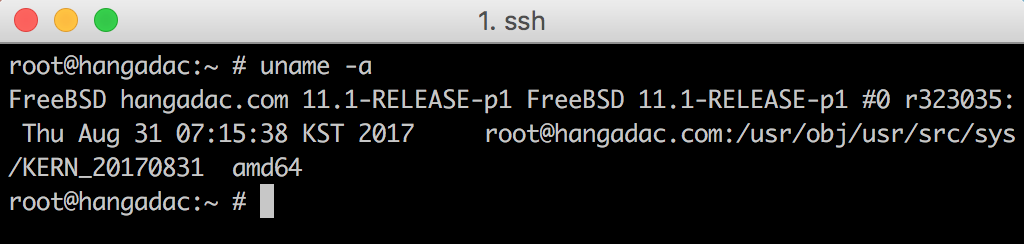 [홈서버] FreeBSD Upgrade (11.0 -> 11.1)
[홈서버] FreeBSD Upgrade (11.0 -> 11.1) 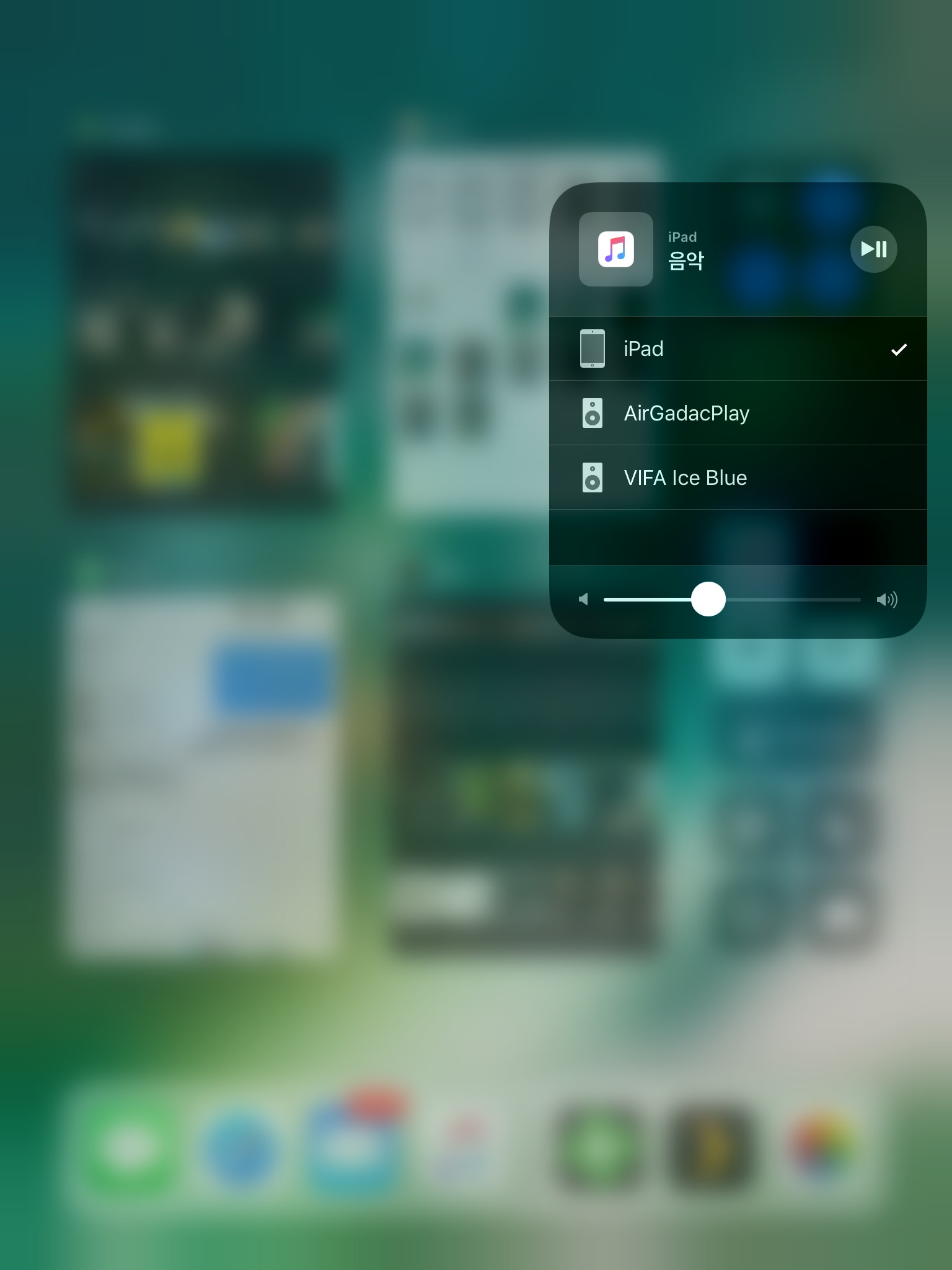 [홈서버] FreeBSD를 광출력 무선 Audio Renderer로 만들기
[홈서버] FreeBSD를 광출력 무선 Audio Renderer로 만들기  [홈서버] Netflix가 부럽지 않다. Emby 혹은 Plex
[홈서버] Netflix가 부럽지 않다. Emby 혹은 Plex  [홈서버] 써보니 편하다, AirPlay
[홈서버] 써보니 편하다, AirPlay 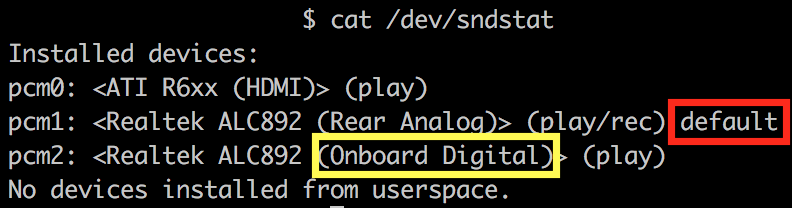 [홈서버] FreeBSD SPDIF Sound out
[홈서버] FreeBSD SPDIF Sound out  매일 등산 2일차 (분당 불곡산 2024-04-14)
매일 등산 2일차 (분당 불곡산 2024-04-14)  매일 등산 1일차 (분당 불곡산 2024-04-13)
매일 등산 1일차 (분당 불곡산 2024-04-13)  [일보우일보] 2023년 12월 29일 – 서울나들이
[일보우일보] 2023년 12월 29일 – 서울나들이  동유럽 배낭여행 5일차 (호엔 잘츠부르크 성)
동유럽 배낭여행 5일차 (호엔 잘츠부르크 성)